Identities
In order to deploy a process that contains services from the Operation Library, you will need to provide an authorization credential known as an identity.
Users can create new identities of following types:
-
HTTPthat is based on eitherbasic,bearerorotherscheme and will be included in HTTP header -
API keythat is based on attaching an api key to the request, either via header or query parameter -
OAuth2that is based on OAuth2 specification and relies on token exchange -
OAuth2 (reuse caller token)that is a special kind of identity based on caller’s identity and allowing to make a request on behalf of to preserve same access rights
At deployment time, if an OAuth2 (reuse caller token) identity type is set, model is validated and warnings are logged in if its structure could lead to mishandling of identity at runtime.
|
Create new identity
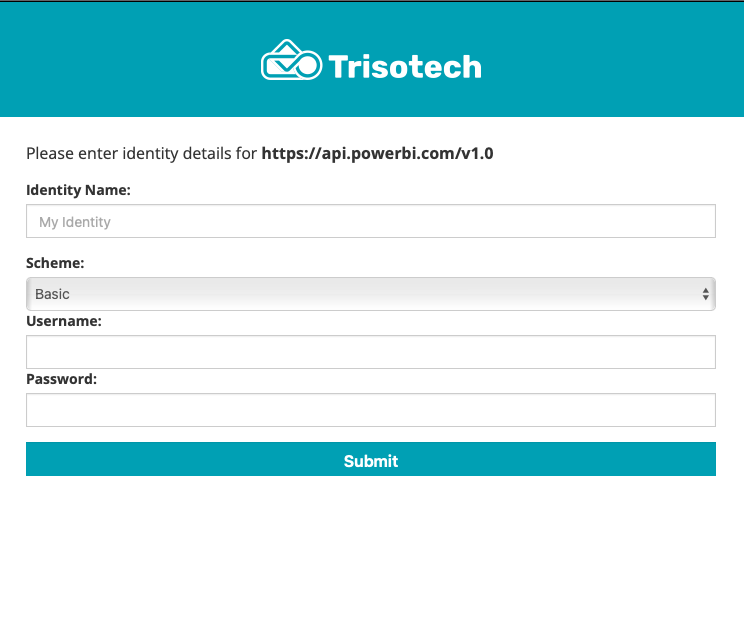
To create new identity, service url needs to be provided and type of identity selected. Based on selected type, additional form will need to be filled.
Identity definitions
Already created identity definitions are presented in a table that can be filtered using the Search field.
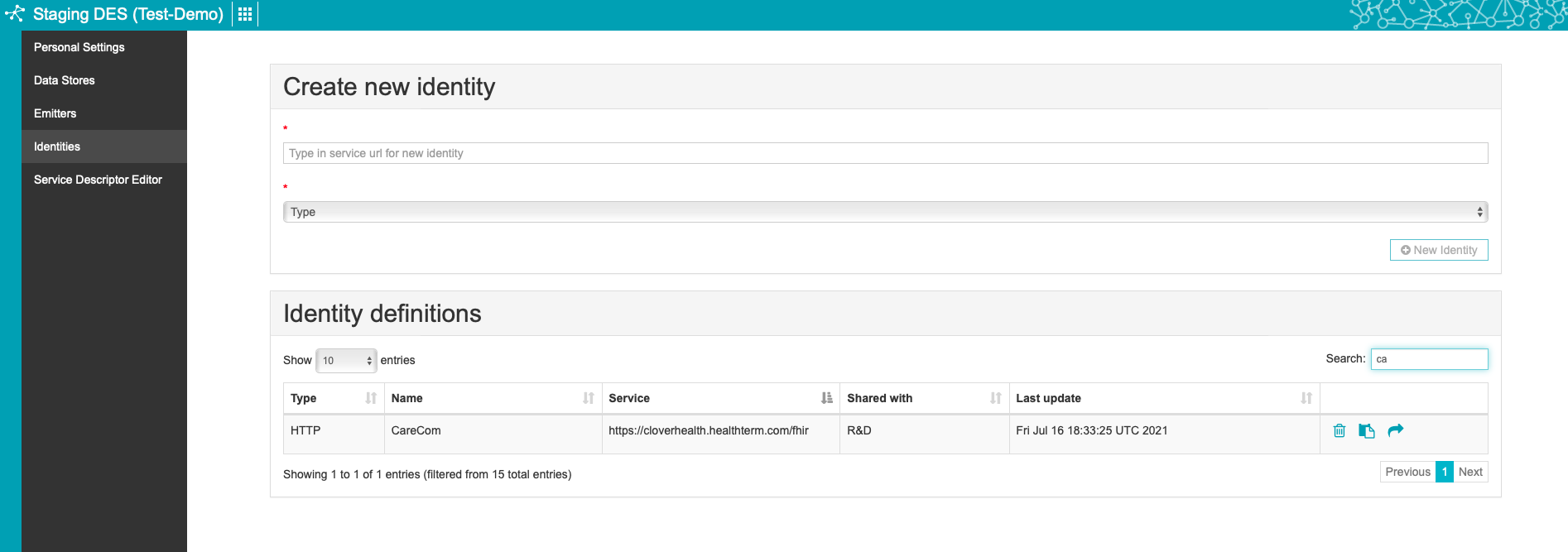
Each identity definition can be
-
permanently deleted
-
shared with group
Identity information is considered sensitive data and by that are not visible after creation. The only attribute that is available is
the id of the identity definition which can later on be used to associate it with services.
|
OAuth2 (reuse caller token)
If a service task is set with an OAuth2 (reuse caller token) identity type as security, a validation of the model is done.
Validation is about iterating over all paths leading to the service task and determine whether or not OAuth2 (reuse caller token) configuration could be properly handled at runtime.
There are a few patterns that would trigger warnings:
-
A timer node, a receive task or an intermediate catch event is set before a service task set with an
OAuth2 (reuse caller token)identity and no user or manual task is set in between -
Concurrent or exclusive paths are set and at least one of them contains a pattern triggering a warning
Also, sub-process and call activity are considered while validating paths.